How can we protect wp-login without any plugins?
Protect with .htaccess and .htpasswd: Create a .htpasswd file:Use an online htpasswd generator to create a user and encrypted password.Save it outside the public directory (e.g., /home/username/.htpasswd).[...]
How to disable REST API access for unauthenticated users?
The WordPress REST API is a powerful tool that allows interaction with your site through HTTP requests. However, there may be instances where you want to restrict[...]
How to disable the REST API in WordPress using PHP code
The WordPress REST API allows applications to interact with your site remotely. However, in certain cases, you might want to disable it to enhance security or limit[...]
How to Protect WordPress from User Enumeration
User enumeration is a common technique used by attackers to identify usernames on WordPress sites. Once usernames[...]
The option “Hide other shipping methods when free shipping is available” is not displayed
If the option "Hide other shipping methods when free shipping is available" is not displayed, you can[...]
Error: Terminating since out of inotify watches. Consider increasing /proc/sys/fs/inotify/max_user_watches
Error: The error means that the system has reached the maximum number of "inotify watches," which limits[...]
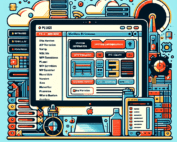
In the WordPress administration panel, how can I see the server’s performance?
In the WordPress administration panel, how can I see the server's performance? Install a system information plugin[...]
A PHP session was created by a session_start() function call. This interferes with REST API and loopback requests. The session should be closed by session_write_close() before making any HTTP requests.
This error occurs because the session_start() function is creating a PHP session, which interferes with REST API[...]
How you can set a default featured image for each post category
In WordPress, you can set a default featured image for each post category by using a snippet[...]
Let’s work together!
Let’s collaborate and bring your dream project to life! Ready to take your business to the next level?
We’re more than just software developers; we’re your partners in success. We’ll work closely with you from concept to implementation to ensure your software meets your expectations.
So, what are you waiting for? Let’s collaborate and make your dreams a reality! Contact us today and we can start discussing your project.